Intellectual Property Theft: A Menace
 Posted On
Posted On
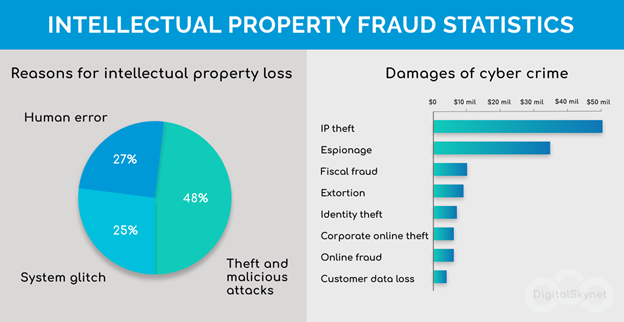
With the advancement of technology and the overreaching effect of cyberspace, cyber crimes have also witnessed a surge. Of these crimes, Intellectual Property (IP) theft is one of the many, which involves stealing copyright, patents, industrial designs, etc., by using the internet and computers as a medium. Copyright and trade secrets like software, secret formula/recipes, music, etc., account to be the most frequently stolen forms of IP, which may result in a huge loss for the company that created it, including the loss of competitive edge and decline of business growth. Stealing of IP does not only affect big enterprises; rather, small startups are also hijacked by it. The 2018 Netwrix IT Risks Report found that small and medium businesses are even more vulnerable to IP theft and cyber espionage than enterprises; however, their losses go unnoticed.
Although the term ‘IP Theft’ is often used in common parlance, it is imperative to note that there can be no theft of IP since IP is immaterial, incorporeal, and intellectual. It would be most appropriate to call it an act of infringement against a relevant form of IP. However, the manifestation of such infringement can be through stealing if the IP is affixed in a tangible medium.
Vulnerable Forms of IP under the Threat of Theft
- Theft of Patents: In general, Patent Infringement occurs when a patent that has been registered and granted by a governmental agency like the US Patent and Trademark Office (USPTO), or the European Patent Office (EPO), or the Indian Patent Office (IPO) is used or applied in the course of trade by another person (infringer) without the authorization of the patent owner.
- Theft of Trademarks: Trademark Infringement ensues when a third party makes unwarranted use of a mark in commercial parlance, usually about similar or competing goods, by affixing a mark that is identical or similar to the registered trademark. The act is pursued to deceive or confuse consumers as to the origin of those goods.
- Theft of Copyright: Generally, Copyright Infringement happens when an original film or artwork or musical work, or software code is reproduced (in whole or part) bearing similarity to the original work or has multiple and identifiable elements copied in a derivative work. The infringing use of technical materials like a handbook directing particular use will also constitute theft if not used with prior authorization.
- Theft of Trade Secrets: Although not usually protected directly through domestic legislation due to the nature of secrets, trade secrets are ordinarily safeguarded through the signing of Non-Disclosure Agreements (NDAs). Therefore, if one party has witnessed another party’s trade secrets following which he or she decides to publicize them contrary to an agreement or apply the same for commercial exploitation without the holder’s permission, he or she would be considered to have violated the NDA, which accounts for contractual breach of obligation, if not directly governed through a statute.
Reasons of Theft of Intellectual Property
- Human Defaults: The most common reason for IP thefts is the errors committed by humans in upholding the requisite information. Employees lose their devices or are negligent in being careful with their gadgets or accidentally send files inclusive of trade secrets to someone outside the company network. These may not happen very frequently, but when they do, there is a huge cost to be paid by the end of it. A much recent example
 involved an Apple employee, a researcher, who got his daughter to work where she filmed the iPhone X for her vlog, which had not been released as of then. It included the footage of the phone with the special employee-only QR codes and a notes app with the code names of unpublished Apple products, which disrupted the business edge of the company.
involved an Apple employee, a researcher, who got his daughter to work where she filmed the iPhone X for her vlog, which had not been released as of then. It included the footage of the phone with the special employee-only QR codes and a notes app with the code names of unpublished Apple products, which disrupted the business edge of the company. - Software Infiltrations: Malicious software sent by criminals often lead to the stealing of credential information. A much-cited example of this is a hacking group called Advanced Persistent Threat 10 (APT 10), which targeted the networks of more than 45 technology companies and US government agencies to steal their information and data concerning several technologies. It enabled them to steal a handful of IP assets and other confidential business information.
- Economic Espionage: It is often resorted to by the employees of an organization who have access to such confidential information. They steal information and trade the same to competitors for benefits. GlaxoSmithKline was a victim of such espionage since its employee, who was a research scientist, had stolen confidential information for the benefit of a Chinese pharmaceutical company.
- Open Innovation: In today’s times, open innovation and collaborations have gained the trend to cooperate in terms of R&D initiatives. This kind of ecosystem allows several players and actors to access the said IP and other sensitive information, thereby increasing the chances of losing such information.
- The Complexity of Supply Chains: Where the number of middlemen increases due to intermingling channels facilitating outsourcing and supplying, the risk of leak of information also increases. Also, poor security practices anywhere in the middle of the supply chain, ranging from an ordinary supplier of raw materials to a logistics provider, can easily act as an open door for infringers and hackers alike to rush for their Intellectual Property Rights (IPRs).
- Digitization of Assets: The digitization of credential data, research, and development-related data, records about IPRs or their assets, or the formulas therein, makes it easier for infringers to access such crucial pieces of information regardless of the physical location of the infringer as well as the target company/entity.

How to Minimize the Risk of IP Theft?
- Identification of Data: Companies seeking to safeguard their IP assets should identify them and the information about the same as the first step to minimizing the risk of IP theft. They should also be well-informed as to who has access to such information by using an automated data classification solution. The same will help to know the data that has been recently created as well as modified.
- Data Security Policy: It is crucial to address the security concerns by creating a security policy to mitigate vulnerabilities while also devising a recovery plan. The same plan of action should be authorized and verified by the legal team as well as the core management team of company executives.
- Proper Scrutiny of Employee Actions: Companies may sign an NDA with their employees; however, the same should not mean that there is no need to scrutinize their actions. All activities, including the interaction of the employees, should be monitored.
- Role of Human Resources Personnel: It’s a good option to coordinate with the HR department and be notified whenever an employee is leaving to watch for suspicious activity, such as copying of data in bulk before they leave and disable their accounts promptly when they are gone to prevent security leaks.
- Provide Adequate Training: The lack of awareness of cybersecurity issues among the employees is a reason for the loss of IP assets. Data sensitivity training concerning their respective profile should be imparted while also addressing password policies, gadget-specific use, and their limitations, how phishing attacks look, etc.
- Consider Registration of IP: Companies should consider obtaining protective designation for their respective IP assets while enforcement should be sought outside one’s domestic jurisdiction to limit the chances of potential infringement through the use of Madrid route, Patent Cooperation Treaties, or separate filings.
- Identify Security Gaps: If you wish to understand how hackers and infringers operate, it is necessary to think like an attacker from his point of view. The same could help reveal hidden or unforeseen security pits and gaps. Therefore, one must not overlook mobile phone or email contacts, recycle bins, employee gadgets facilitated by the company for official purposes, old CCTV recordings, etc.
Conclusion
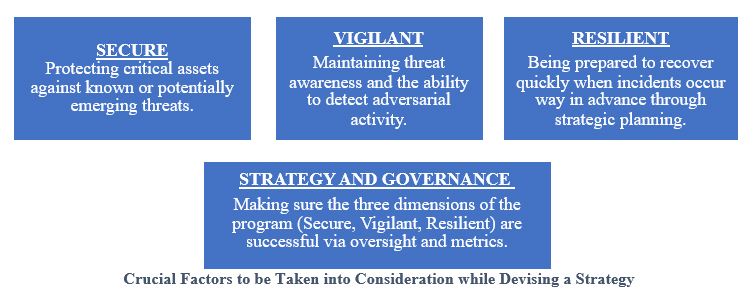
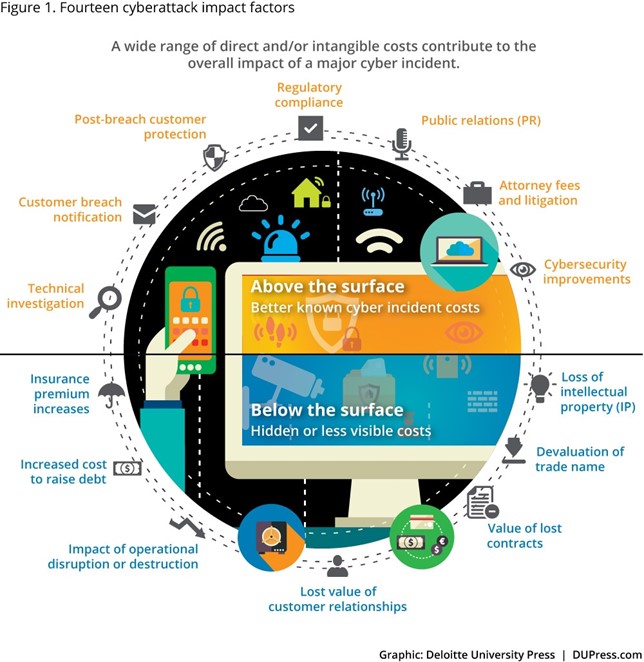
IP assets help in driving a company’s competitiveness and growth. Therefore, trademark, patent, trade secret, and copyright protection should be an integral part of every security strategy being opted by an entity. Building a strong line of defense requires a company-wide involvement of all actors, from regular users and employees to top executives.
Acknowledging the fact that risks are constantly rising, entities should ensure they have proper security policies in place concerning sensitive data; and continue working in consortium with their employees to minimize risks coming from insiders and outsiders alike.
In furtherance of the same, building true resilience requires a firm-wide strategic focus from the top of the organization on the overall business risk that IP cyber theft poses. As noted above, knowing what IP assets an entity possesses, where and how such assets are safeguarded, and incorporating IP cyber protection into the overall IP management program should be integral to their strategy. ✅ For more visit: https://www.kashishipr.com/